Compliance you can measure.Oversight you can defend.
With Lexalign, depository institutions can recruit their customers at scale into compliance and risk management, for fraud prevention, demonstrable oversight and confident growth.
ON DEMAND WEBINAR
Preparing + Empowering Your ACH Originators for Nacha's 2026 Fraud Monitoring Requirements
Nacha's Fraud Monitoring Rules expand expectations for what financial institutions when it comes to non-consumer Originator oversight / With Phase 1 already in effect and Phase 2 enforcement beginning June 22, 2026, the question is no longer whether to act, but how.
WATCH
4 Boxes to Check for Nacha's 2026 Fraud Monitoring Rules
Learn the full scope of what the Rules require and the toolkit you'll need.

FREE GUIDE
Download the Guide: 4 Boxes to Check for Nacha's 2026 Fraud Monitoring Rules
Fraudsters exploit the least secure channel:
your customers.
Fraudsters are exploiting gaps in your customers’ operations and sophistication that are invisible to you.
$196B
estimated total U.S. fraud and scam losses in 2024, with USD 15.6 billion from account takeover alone, where bad actors exploit compromised credentials and customer operations to initiate transactions that look legitimate to the bank.
(FTC 2024–2025; Javelin 2025 Identity Fraud Study)
$5.75
what every $1 lost to fraud actually costs a U.S. financial institution in 2025, up from $4.00 in 2021. A single $100K customer-side fraud event becomes a $575K hit to your P&L.
(LexisNexis 2025 True Cost of Fraud Survey)
71%
the share of all fraud incidents and dollar losses now driven by unauthorized-party schemes — credential theft, account takeover, and system compromise — up from 48% just one year earlier. The fraud is migrating to wherever customer controls are weakest.
(PYMNTS/Block 2025 State of Fraud and Financial Crime)
Cost of fraud is compounded when participants in the payment system aren't compliant.
Banks rely on 10s of millions of SMB clients to ensure that 10s of trillions of dollars in digital payments and deposits are properly authorized, compliant and secure.
Banks use Lexalign's automated solutions to manage risk and compliance at scale.
Lexalign delivers a risk management platform to customers and advance warning to banks, enabling you to move from reactive, laborious and costly defense to proactive, efficient, data-based routines.
Fraud Prevention
True Compliance
No Integration Needed
Data-powered Risk Management
Audit-ready Records
Easy Set-up in Hours
HowLexalignWorks
3 Easy Steps
STEP 1
Conduct a Compliance Audit
On a dedicated “Compliance Dashboard,” Lexalign takes each of your customers through the fundamental step in risk management: a self-assessment of their operations against the rules and risk framework to determine what rules apply and where they deviate. No background expertise required.
STEP 2
Deliver a Risk Compliance Program
Next, Lexalign instantly furnishes your customers with critical information they need to manage their risk and compliance: an Audit Report (with an inventory of regulated activities, a gap analysis and an action plan); a customized Policy, Procedures and Training packet; a dynamic Remediation Checklist.
STEP 3
Receive Actionable Compliance Records
You instantly get essential records that demonstrate your risk management at scale, as well as scoring and analysis that enable proactive, low-effort, targeted interventions to mitigate risk and strengthen your customer relationship.
Banks that use Lexalign have realized...
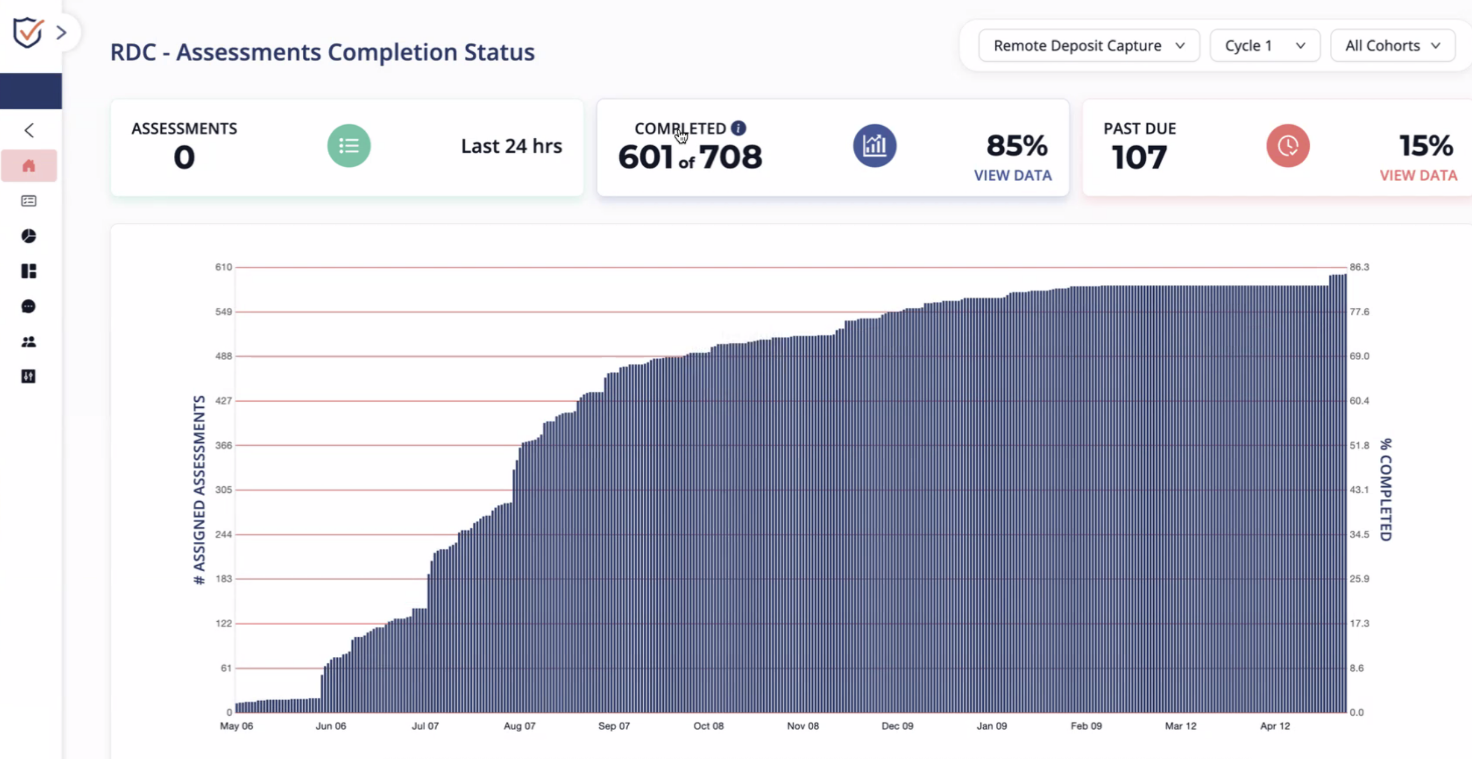
80%
of customers complete their assigned assessment.
95%
of customers open their audit reports
100%
Resolution of related audit exceptions and findings
Plus, banks achieve higher customer engagement, retention, deposits, and sales, as well as growth with demonstrable compliance even beyond their footprint.
Transform Fraud Prevention: Why This Matters
Fraud that targets customers as the access point is fast becoming the next crisis in banking. According to the latest AFP Payments, Fraud and Control Survey Report, 4 out of 5 customers report being attacked, and fraud is rising over all payment channels, including ACH checks and wires.
To fraudsters, the customer is now the front door of the bank, and according to Nacha, credit-push fraud has become the predominant form. Nacha has called for a New Risk-Management Framework For Credit-Push Fraud, one in which “all participants in the payment system, whether the ACH Network or elsewhere, have roles to play in working together to combat fraud.” All participants necessarily includes the non-consumer customer as the starting point.
But it is not feasible to effectively assess and empower the security and compliance of customer operations at scale using legacy manual approaches. We created Lexalign to solve this systemic gap.
News & Resources
February 3, 2026
From Guidance to Enforcement: The Real Consequences of Not Preparing for Nacha’s Fraud Monitoring Rules
No bank wants to spend money on a new solution—especially in an environment where budgets…
0 Comments10 Minutes

January 9, 2026
The “4 Boxes” to Check for Audit-Ready Compliance
As financial institutions enter 2026, one topic continues to surface in payments, risk,…
0 Comments13 Minutes

CONTACT US
Get Started Today
Join leading financial institutions in transforming your risk management approach. Discover how Lexalign can help you achieve compliance excellence and protect your organization from fraud.










